UK 'near the bottom of league tables' on IoT security
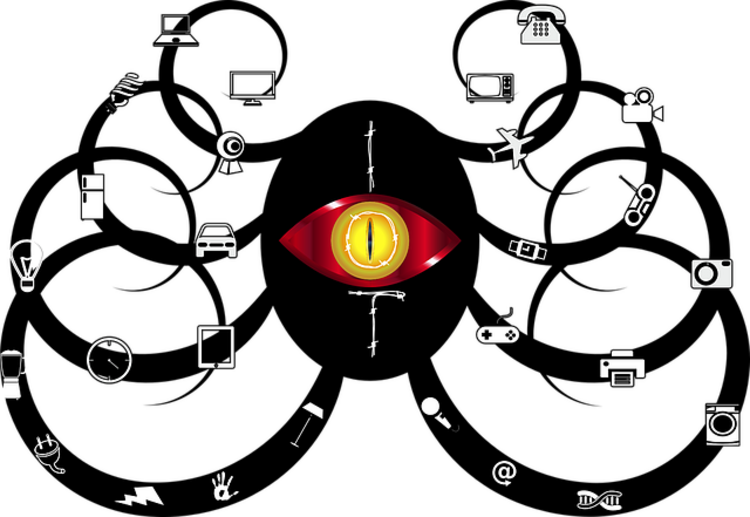
A massive six in ten UK organisations can’t tell If their IoT devices have been breached by hackers or not, according to a new study by Gemalto.
Flipping the figures around, while 42 percent of UK organisations can detect IoT device breaches, this is the second lowest in Europe after France, at 36 percent. This might be connected to the fact that UK spending on IoT protection is lower than the global average (11 percent of IoT budgets).
Jason Hart, CTO of data protection at Gemalto, told SC Media UK: "The simple fact is that lack of investment in properly securing IoT devices means that the UK not only continues to struggle on IoT security, but that it’s left itself wide open to attack from cyber criminals."
He added: "British organisations must start looking at how they protect themselves, focussing on spending in the right areas in order to protect what matters with the increasing amounts of sensitive data IoT devices now produce. This means investing in applying the correct security controls such as encryption, key management and user and device authentication which enables that correct level of security to protect the data whether it’s in transit or at rest and accessing both the data and the device at all times."
On the bright side, awareness is growing, with spend on protection rising in just the last year, from 11 percent of IoT budget in 2017 to 13 percent now, while nearly three times as many respondents now see IoT security as an ethical responsibility (14 percent), compared to a year ago (four percent), according to Gemalto’s survey of 950 IT and business decision makers globally.
Organisations worldwide are seeking help when securing the IoT, with most businesses (95 percent) in the global study asking for more security regulations in the IoT industry.
With such a big task in hand, businesses are calling for governmental intervention because of the challenges they see in securing connected devices and IoT services. This is particularly mentioned for data privacy (38 percent) and the collection of large amounts of data (34 percent). Protecting an increasing amount of data is proving an issue, with only three in five (59 percent) of those using IoT and spending on IoT security admitting they encrypt all of their data.
Joseph Carson, chief security scientist at Thycotic, told SC: "These statistics on the shocking state of IoT security come as no surprise at all – many organisations do not even know they have IoT deployed. This confirms they are not actively discovering IoT devices or even attempting to manage them, so it is not surprising that they are not being properly secured, or even worse, the default security settings are not changed including the default passwords."
He added: "Many organisations are spending blindly on IoT devices as suppliers do not make it clear what security features are available and they mostly focus on ease of use, sacrificing security by design. Regulations are surely coming and will likely force vendors to display, inform or even go as far as ensuring security best practices are easy to enable and use."
The UK Government introduced the Internet of Things (IoT) security code of practice (CoP) for manufacturers and developers last last year, and although the guidelines have been well received, implementing them will take some time. Of those firms that have committed to implementation, HP and Centrica Hive have said it may be 2021 before they can fully implement the CoP.
Anna Russell, VP at comforte AG, told SC that increased regulation was likely.
"The numbers send two very clear messages," she said. "Firstly, the UK needs to step up in terms of their IoT investments and efforts. Secondly, with such strong support for regulations on IoT security, it is only a matter of time until we see something emerging here. Until such a new regulation comes to life, organisations worldwide should focus at least to make sure that they have a data-centric security strategy in place for protecting sensitive data in their IoT environments."
In the interim, the study found that the industry is seeking to self-regulate, with a surprising contender emerging. Adoption of blockchain has doubled from 9 percent to 19 percent in the last 12 months. Not only that, but a quarter (23 percent) of respondents to the Gemalto survey believe that blockchain technology would be an ideal solution to use for securing IoT devices, with 91 percent of organisations that don’t currently use the technology likely to consider it in the future.
Chris Doman, security researcher at AlienVault, was not impressed: "I don't see how adding blockchain to IoT will make the devices any more secure, I'd hoped we were past the point of saying blockchain will fix everything! The main problems we see are known default passwords on things like webcams and other devices, and we see attackers regularly scanning the internet to find them. It's unlikely things will improve until device manufacturers are more liable for security failures."
source scmagazineuk
Industry: Cyber Security News

Latest Jobs
-
- Public Sector Cyber Security Sales | UK
- England
- N/A
-
Public Sector Cyber Security Sales | UK UK | Remote / Hybrid A cyber security provider is seeking a Public Sector Sales professional to drive growth across UK government and public sector organisations. Must have current Cyber Security sales experience. Responsibilities Generate new business selling cyber security solutions into UK public sector Build relationships with CIO, CISO and senior technology stakeholders Manage the full sales cycle from opportunity to contract close Develop pipeline across central government, local government and public sector bodies Support bids, tenders and framework opportunities Experience Proven cyber security sales experience in the UK Track record selling into public sector organisations Familiarity with CCS, G Cloud or other government frameworks Strong stakeholder engagement and deal management skills Location UK based Security Requirements Eligible to obtain UK Security Clearance
-
- Security Architect | MoD - Security Cleared. OUTSIDE IR35 | Hampshire
- N/A
- Outside IR35
-
Security Architect | MOD | Security Cleared | Outside IR35 | Hampshire Commutable The successful candidate must be willing to undergo DV Clearance, ideally already holding active clearance. You will produce high and low level security architecture documentation, guiding and validating designs for systems deployed within sensitive environments. The role requires providing specialist security input into solution design, service transition and change initiatives, working closely with engineering, operations, client and third party stakeholders. You must have current hands on architectural experience, including VMware secure platform design and virtualisation architecture, alongside AWS expertise. This is an outside IR35 contract- 6 month rolling. Part of a longer term MoD project
-
- Active Directory | RBA engineer | UK Remote | SC Clearable
- United Kingdom
- N/A
-
Technical Active Directory (AD) and RBA specialist needed to play a key part in complex, enterprise scale Active Directory and access transformation programmes. You will work alongside senior team, helping reshape access models, modernise legacy directory structures and strengthen security posture across secure environments. This is hands on delivery within high impact projects where your work directly improves access control, compliance and operational resilience. Active UK Security Clearance required. This is a remote role with client travel. Implementation of Role Based Access Control across large AD estates Restructuring complex permission models, security groups and delegated access Supporting domain controller upgrades and core directory improvements Applying security hardening standards and remediating audit findings Enhancing authentication, policy and access governance frameworks Troubleshooting and resolving technical AD challenges within live environments Producing robust technical documentation and identifying project risks You must have the following technical experience Enterprise Active Directory administration Role Based Access and permission remediation OU design and governance Group Policy management Security group delegation models DNS and DHCP services Kerberos authentication / NTLM PowerShell scripting and automation Azure AD | Entra ID Hybrid identity environments Identity Governance PAM
-
- Identity and Access Management Consultant (Saviynt & Microsoft Entra) | UK
- United Kingdom
- N/A
-
Role summary Technical IAM consultant delivering identity governance and cloud identity solutions to enterprise clients. What you will do Implement / Configure / Deploy Saviynt IGA / Microsoft Entra solutions: Lead technical workshops, gather requirements and translate into solution designs. Troubleshoot complex issues, support testing and deployments. Produce technical artefacts and configuration guides. Key skills Hands-on Saviynt IGA experience (workflow, connectors, access governance). Strong practical knowledge of Microsoft Entra ID / Azure AD identity and access controls. Understanding of identity protocols (SAML, OAuth, OpenID Connect) and hybrid identity. Experience with APIs / REST for integrations and automation. What we are looking for Proven delivery experience in IAM / IGA projects, preferably in consulting. Confident communicator with client-facing delivery exposure.