BlackBerry licenses security tech to IoT device makers
.png)
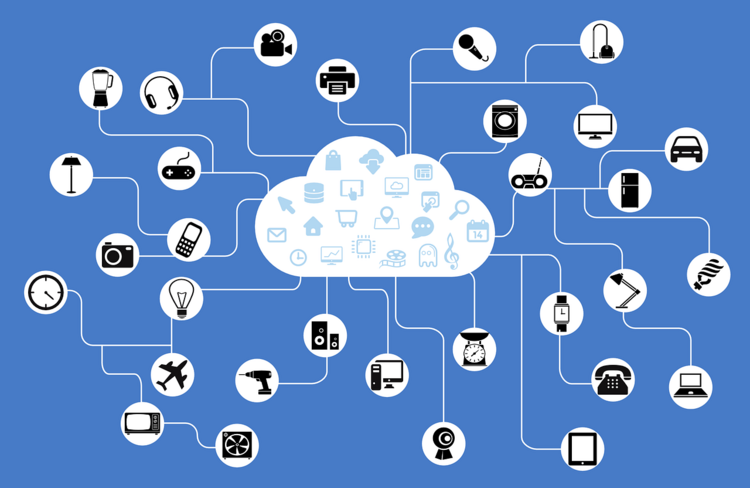
BlackBerry is to license its secure software development technology to the makers of internet-connected devices to boost IoT security
When asked about future purchases, respondents said they were more likely to choose a product or do business with a company that had a strong reputation for data security and privacy.
To address this concern, BlackBerry announced at the Consumer Electronics Show (CES) in Las Vegas that it is to license its trusted software framework to enable device makers to build smart products securely without having to develop their own technology and cyber security expertise.
Once developed, BlackBerry’s team of cyber security experts will review each device, awarding BlackBerry Secure certification to show that the required level of data security and trust has been met.
“2019 will be the year consumers will begin to vote with their wallets and seek out products that promise a higher level of security and data privacy,” said Alex Thurber, senior vice-president and general manager of mobility solutions at BlackBerry.
“IoT device manufacturers can address security and privacy concerns head-on and stand out in the cluttered IoT space by bringing to market ultra-secure products that consumers, retailers and enterprises want to buy and use,” he said.
Thurber described the initiative as “a pivotal point” in BlackBerry’s software licensing strategy. “It underscores BlackBerry’s evolution from providing the most secure smartphones to delivering the trusted security for all smart ‘things’,” he said.
From today, device makers will have the choice of three “feature packs” which build on each other and provide various levels of management and control.
The BlackBerry Secure Enablement Feature Pack offers secure manufacturing and product lifecycle management features.
This means BlackBerry will provide a manufacturing station that provides a hardware root of trust and is connected to the company’s Network Operation Centre that is monitored 24/7 for uptime and reliability. During manufacturing, a BlackBerry identity key is injected into the hardware and recorded on a secure server. At launch and periodically throughout the product’s lifecycle, checks will be performed to verify that the two keys match. If they do not, the device no longer boots.
The BlackBerry Secure Foundations Feature Pack is aimed at enabling product suppliers to harden the operating system kernel and lock down software being executed.
This includes secure boot and ARM Trustzone technology to generate, use and store encryption keys used for various software operations. It also includes the BlackBerry Integrity Detection service which generates real-time “health” reports that can be accessed by users and trusted third-party applications.
The BlackBerry Secure Enterprise Feature Pack is aimed at devices that will be used in regulated or restricted environments as it enables deeper management and control beyond what is standard in Android Enterprise.
Through extended device management policies deployed on the device, BlackBerry said enterprises could protect their data by controlling what can be accessed via device debug interfaces, communication protocols such as Bluetooth, and cellular, Wi-Fi and GPS communication channels.
In 2018, IoT technology firms began signing up to a UK code of practice to strengthen the security of internet-connected devices. The code is expected to form the basis of an international standard.
In October, the UK published a voluntary code of practice (CoP) to help manufacturers boost the security of internet-connected devices that make up the internet of things (IoT).
Tech companies HP and Centrica Hive were the first to commit to implement the CoP by 2021. The code is aimed at encouraging innovation while ensuring tech consumers are safe by addressing potential security vulnerabilities at the design stage.
Although the CoP is aimed at consumer products, the UK government hopes it will establish standards and principles that will filter through to the industrial, enterprise and other IoT markets. Also, government departments plan to engage with individual sectors about industry-specific IoT security issues.
In view of the risk posed by IoT devices, the UK is leading global efforts to improve the security of internet-connected devices by encouraging device makers to embed security into the design of new technology rather than bolt it on afterwards.
source computerweekly
Industry: Cyber Security News
