Bugs in Samsung IoT Hub Leave Smart Home Open To Attack
Researchers found 20 flaws in Samsung’s SmartThings Hub controller – opening up supported third-party smart home devices to attack.
Researchers found 20 vulnerabilities in Samsung’s SmartThings Hub, allowing attackers to control smart locks, remotely monitor the home via connected cameras and perform other alarming functions.
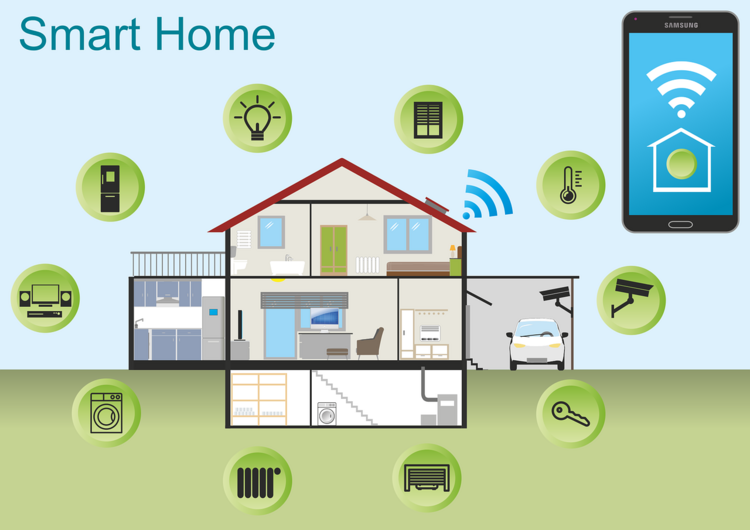
Cisco Talos researchers, who published a technical breakdown of the vulnerabilities on Thursday, said each of the flaws are located in Samsung’s centralized controller, a component that connects to an array of IoT devices around the house – from light bulbs, thermostats, and cameras. SmartThings Hub is one of several DIY home networking devices designed to allow homeowners to remotely manage and monitor digital devices.
“Given that these devices often gather sensitive information, the discovered vulnerabilities could be leveraged to give an attacker the ability to obtain access to this information, monitor and control devices within the home, or otherwise perform unauthorized activities,” researchers said in a report.
SmartThings Hub uses a Linux-based firmware and allows for communications with various IoT devices using various wireless standards Zigbee, Z-Wave and Bluetooth. SmartThings supports a broad spectrum of third-party products- from Philips Hue smart lightbulbs, to Ring video doorbells, as well dozens more smart home products sold under the brands GE, Bose and Lutron.
The breadth of potentially impacted products means an attacker could hack an array of connected home devices allowing adversaries to disable smart locks, turn off motion detectors, shut down smart plugs, control thermostats or even cause physical damage to appliances.
A Samsung spokesperson told Threatpost patches have been deployed that fix the bugs. “We are aware of the security vulnerabilities for SmartThings Hub V2 and released a patch for automatic update to address the issue. All active SmartThings Hub V2 devices in the market are updated to date,” Samsung said.
Separate to Cisco Talos, Samsung released a firmware advisory for Hub V2 devices on July 9.
Several vendors whose third-party products are supported by SmartThings including Philips Hue, Bose, Lutron and Ring didn’t respond to requests for comment from Threatpost.
Multiple Attack Chain Scenarios
Successful exploitation of vulnerabilities is not trivial. All require an attacker to chain a number of existing vulnerabilities together, according to the report.
“When considering the severity of vulnerabilities, it is essential to keep in mind that they might be used as part of a chain, as this would significantly elevate their severity,” researchers said.
There are three different attack chains that could be exploited by hackers to penetrate home devices, researchers said. The first is a remote code execution (RCE) vulnerability – the most dangerous of the three because it can be exploited without prior authentication and can be performed remotely.
Attack One
This RCE chain attack impacts the “video core” HTTP server of the hub, and allows attackers to inject HTTP requests into this process from a network. The vulnerability (CVE-2018-3911) exists within the communications (via Port 39500) present between the hub and the remote servers it communicates with. The vulnerability is essentially an exploitable HTTP header injection bug that enables attackers to send specially crafted HTTP requests to impacted devices.
Researcher note, these injected requests are only semi-controlled – so to take full advantage of the attack, a bad actor would also need to exploit bugs (vulnerabilities CVE-2018-3907 to CVE-2018-3909) within the REST request parser of the “video core” process, which modifies the path of an HTTP request.
Finally, an attacker could close out the attack chain by leveraging a bug (CVE-2018-3902) that exists in the camera “replace” feature of video-core’s HTTP server. They would send an HTTP request leading to a buffer overflow attack on the stack.
Attacks Two, Three
The other two attack chains require the attacker to gain prior authentication, researchers said. One of these attacks enables remote code execution via a vulnerability (CVE-2018-3879) enabling authorized attackers to execute SQL queries against a database inside the device.
When used alone, this flaw only allows attackers to alter the database – but an array of other memory corruption vulnerabilities (CVE-2018-3880, CVE-2018-3906, CVE-2018-3912 to CVE-2018-3917, and CVE-2018-3919) that exist in SmartThings Hub allow for executing arbitrary code in the network after exploiting the first bug, researchers said.
The vulnerability CVE-2018-3879 can also be leveraged in the final chain attack, which allows for remote information leakage. This vulnerability can be used to create an empty file anywhere inside the device.
Attackers can then leverage denial of service bug CVE-2018-3926, which exists within the ZigBee firmware update process present within the “hubCore” binary used by the SmartThings Hub. Once the empty file is created this bug will cause the “hubcore” process to crash, triggering an information leak bug (CVE-2018-3927) that can be captured from the network.
“By chaining these 3 vulnerabilities in order, an attacker can obtain a memory dump of the `hubCore` process, which contains most of the core logic, and consequent sensitive information, of the Hub,” researchers said.
While Samsung’s updates have been pushed out automatically, researchers recommended that users verify the updated version has actually been applied to devices to ensure that they are no longer vulnerable.
“While devices such as the SmartThings Hub are typically deployed to provide additional convenience and automation to users, special consideration must be made to ensure that they are configured securely, and updated when new firmware updates are made available by the manufacturer,” they said.
Source: threatpost

Latest Jobs
-
- Public Sector Cyber Security Sales | UK
- England
- N/A
-
Public Sector Cyber Security Sales | UK UK | Remote / Hybrid A cyber security provider is seeking a Public Sector Sales professional to drive growth across UK government and public sector organisations. Must have current Cyber Security sales experience. Responsibilities Generate new business selling cyber security solutions into UK public sector Build relationships with CIO, CISO and senior technology stakeholders Manage the full sales cycle from opportunity to contract close Develop pipeline across central government, local government and public sector bodies Support bids, tenders and framework opportunities Experience Proven cyber security sales experience in the UK Track record selling into public sector organisations Familiarity with CCS, G Cloud or other government frameworks Strong stakeholder engagement and deal management skills Location UK based Security Requirements Eligible to obtain UK Security Clearance
-
- Security Architect | MoD - Security Cleared. OUTSIDE IR35 | Hampshire
- N/A
- Outside IR35
-
Security Architect | MOD | Security Cleared | Outside IR35 | Hampshire Commutable The successful candidate must be willing to undergo DV Clearance, ideally already holding active clearance. You will produce high and low level security architecture documentation, guiding and validating designs for systems deployed within sensitive environments. The role requires providing specialist security input into solution design, service transition and change initiatives, working closely with engineering, operations, client and third party stakeholders. You must have current hands on architectural experience, including VMware secure platform design and virtualisation architecture, alongside AWS expertise. This is an outside IR35 contract- 6 month rolling. Part of a longer term MoD project
-
- Active Directory | RBA engineer | UK Remote | SC Clearable
- United Kingdom
- N/A
-
Technical Active Directory (AD) and RBA specialist needed to play a key part in complex, enterprise scale Active Directory and access transformation programmes. You will work alongside senior team, helping reshape access models, modernise legacy directory structures and strengthen security posture across secure environments. This is hands on delivery within high impact projects where your work directly improves access control, compliance and operational resilience. Active UK Security Clearance required. This is a remote role with client travel. Implementation of Role Based Access Control across large AD estates Restructuring complex permission models, security groups and delegated access Supporting domain controller upgrades and core directory improvements Applying security hardening standards and remediating audit findings Enhancing authentication, policy and access governance frameworks Troubleshooting and resolving technical AD challenges within live environments Producing robust technical documentation and identifying project risks You must have the following technical experience Enterprise Active Directory administration Role Based Access and permission remediation OU design and governance Group Policy management Security group delegation models DNS and DHCP services Kerberos authentication / NTLM PowerShell scripting and automation Azure AD | Entra ID Hybrid identity environments Identity Governance PAM
-
- Identity and Access Management Consultant (Saviynt & Microsoft Entra) | UK
- United Kingdom
- N/A
-
Role summary Technical IAM consultant delivering identity governance and cloud identity solutions to enterprise clients. What you will do Implement / Configure / Deploy Saviynt IGA / Microsoft Entra solutions: Lead technical workshops, gather requirements and translate into solution designs. Troubleshoot complex issues, support testing and deployments. Produce technical artefacts and configuration guides. Key skills Hands-on Saviynt IGA experience (workflow, connectors, access governance). Strong practical knowledge of Microsoft Entra ID / Azure AD identity and access controls. Understanding of identity protocols (SAML, OAuth, OpenID Connect) and hybrid identity. Experience with APIs / REST for integrations and automation. What we are looking for Proven delivery experience in IAM / IGA projects, preferably in consulting. Confident communicator with client-facing delivery exposure.